The Research Team found the error on Monday that some cyber threat actors are exploring the Google Analytics Service and also find that they are stealing the Credit card details and it mainly affects the e-commerce website.
After Finding an article on HackersNews, Perimeter, Kaspersky and the final one are Sansec, the cyber attacker has now injecting data-stealing script inside the website to compromise the website as similar to the tracking code generated by the Google analytics for their own account and collecting the payment information entered by the users where the Content Security Policy (CSP) are enforced for maximum.
While the Kaspersky team mentioned, “ The threat actors are injecting malicious scripts which collect all the data which is entered by the user and then it is sent via Google analytics”. The result came that the attackers could access the stolen data in their Google Analytics account.
Many of the cybersecurity companies claim that they find even more than two dozen infected websites across the North and South America and some parts of the European countries where the company like Food products seller, Cosmetics, digital equipment, and the car or motorbike spare part.
Analysis
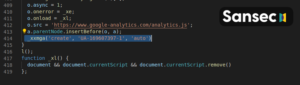
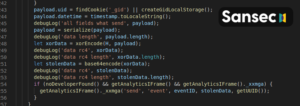
As the Sansec analyzed the tracking of this novel campaign since march 17th.There are several dozen stores and have been injected with the loader, which runs on google open storage platform
Fiirebasestorage.googleapis.com
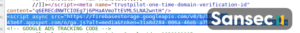
The threat actor hinges on the premise and the e-commerce websites use Google’s web analytics services which track the visitors and the whitelisted domains that are associated with the Content Security Policy(CSP).

The CSP plays an important role in creating security measures that help to detect and mitigate the cyber threat actors to steam from cross-site scripting Vulnerabilities and the other forms of the code script which is used for injecting in attacks and also include those various Magecart groups.
When we talk about the security features which allow webmasters to define a set of domains then the web browser should have been allowed to instruct with a specific URL and there the untrusted code execution should be prevented.
“The Source of the problem is that the CSP rule system is not enough as the” PerimeterX researcher said. When you recognize and stop the above malicious Javascript request and require an advanced visibility solution that can detect the access and exfiltration of sensitive user data like email address and password.
The method used for data harvest that mainly uses the small piece of javascript code that transmits the collected details which consist of Credentials and payment information which can be created through events and other parameters that Google Analytics uses uniquely and identifies the action performed on the site.
The Kaspersky Note in the Blog “ When “Administrator Write*.google-analytics.com which are found in the Content security policy(CSP) Header(Basically used for the list resources from which the third party code can be downloaded) and that also allows the services to collect the data. The more facts that the attack can be implemented and executed without downloading code from the external sources.
To make the attacks more hidden the cyber threats are also as certain as the developer mode-The the feature that’s often used to spot network requests and security errors which are among the other things.
As the researcher mentioned about “ A possible solution would come from the adaptive URLs which can add the ID as part of the URL or subdomains that can allow admins to set CSP rules which restrict data exfiltration to the other accounts”
As the customer is unfortunate that there isn’t much you can do to safeguard yourself from form jacking attacks/ Turning the developer mode in browser can help when you make online purchases
But take care of unauthorization access and purchase or theft of identity.
Found this article informative? Follow Vednam on Facebook, Twitter, Mix, Tumbler, and Linkedin to know more exclusive content we post.